Cryptography
-


How does HTTPS encryption work?
Jan 26, 2023 by Lane WagnerHypertext Transfer Protocol Secure or HTTPS is an extension of the HTTP protocol. HTTPS secures the data transfer between client and server by encrypting all of the information communicated.
-
What is Cryptography? A Complete Overview
Sep 08, 2021 by Lane WagnerWhat is cryptography? 🔗 Simply put, Cryptography provides a method for secure communication. It stops unauthorized parties, commonly referred to as adversaries or hackers, from gaining access to the secret messages communicated between authorized parties.
-


Intro to the One-Time Pad Cipher
Jun 28, 2021 by Lane WagnerIn cryptography, the one-time pad, or OTP is a way of encrypting information so securely that it’s impossible to be cracked.
-
What Is Entropy In Cryptography?
Sep 28, 2020 by Lane WagnerIf you’re familiar with the laws of thermodynamics, you may recognize the second law as the one that deals with entropy.
-
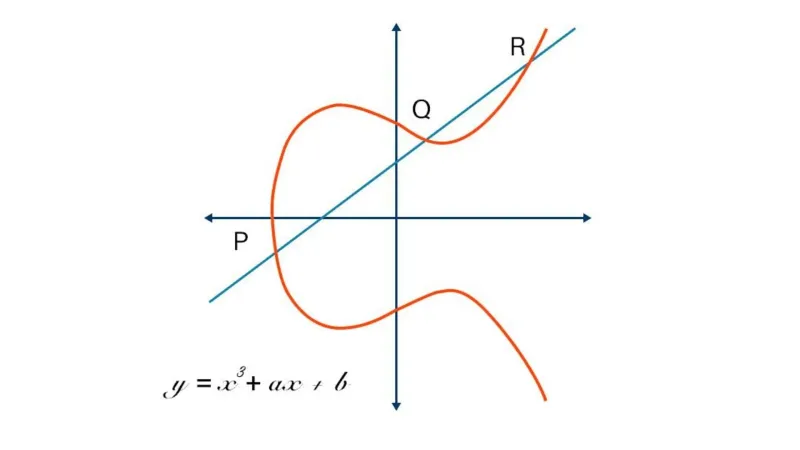
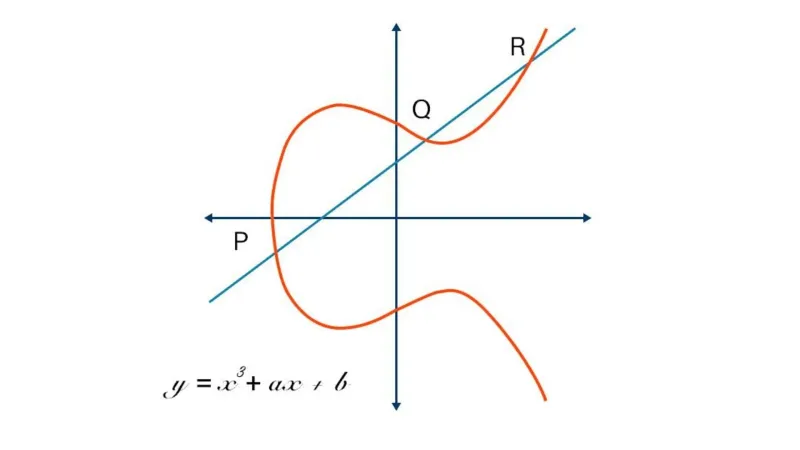
Elliptic Curve Cryptography: A Basic Introduction
Sep 17, 2020 by Lane WagnerElliptic Curve Cryptography (ECC) is a modern public-key encryption technique famous for being smaller, faster, and more efficient than incumbents.
-
Is AES-256 Quantum Resistant?
Sep 10, 2020 by Lane WagnerWith quantum computers getting more powerful each year, many worry about the safety of modern encryption standards.
-


Bcrypt Step by Step
Aug 24, 2020 by Lane WagnerBcrypt is a key derivation function, which can be thought of as a special kind of hash function.
-
(Very) Basic Intro to Lattices in Cryptography
Aug 21, 2020 by Lane WagnerLattice-based cryptography, an important contender in the race for quantum-safe encryption, describes constructions of cryptographic primitives that involve mathematical lattices.
-
Shamir's Secret Sharing Step-By-Step
Aug 18, 2020 by Lane WagnerAdi Shamir’s Secret Sharing is a cryptographic algorithm that allows distinct parties to jointly share ownership of a single secret by holding shares.
-


HMAC and MACs - The Inner Workings of JWTs
Aug 05, 2020 by Lane WagnerHMACs and MACs are authentication codes and are often the backbone of JWT authentication systems. A Message Authentication Code (MAC) is a string of bits that depends on a secret key and is sent with a message to prove the message wasn’t tampered with.
-
(Very) Basic Intro to PGP (GPG)
Jul 27, 2020 by Lane WagnerPGP, or its open-source alternative, GPG, is a program used to encrypt data such that only an authorized party can decrypt it.
-


(Very) Basic Intro to the Scrypt Hash
Jul 25, 2020 by Lane WagnerScrypt is a slow-by-design key derivation function designed to create strong cryptographic keys. Simply put, the purpose of the Scrypt hash is to create a fingerprint of its input data but to do it very slowly.
-
What is SHA-256?
Jul 08, 2020 by Lane WagnerSHA-2 (Secure Hash Algorithm 2), of which SHA-256 is a part, is one of the most popular hash algorithms around.
-


(Very) Basic Intro To White-Box Cryptography
Apr 27, 2020 by Lane WagnerWhite-box cryptography combines methods of encryption and obfuscation to embed secret keys within application code. The goal is to combine code and keys in such a way that the two are indistinguishable to an attacker, and the new “white-box” program can be safely run in an insecure environment.
-


AES-256 Cipher – Python Cryptography Examples
Feb 06, 2020 by Lane WagnerWant to encrypt text with a password or private key in Python? AES-256 is a solid symmetric cipher that is commonly used to encrypt data for oneself.
-


Will Banning Cryptography Keep the Country Safe?
Feb 05, 2020 by Lane WagnerPoliticians in the United States have been claiming recently that end-to-end encryption is certainly too dangerous to permit.
-


Is Open-Source Cryptography Really Secure?
Jan 30, 2020 by Lane WagnerThe purpose of cryptography is to keep information private, and the purpose of open-source is to make code public… So we shouldn’t open-source our cryptography algorithms right?
-


Hashing Passwords - Python Cryptography Examples
Jan 29, 2020 by Lane WagnerBuilding a from-scratch server or using a lightweight framework is empowering. With that power comes responsibility, specifically the responsibility to securely store user’s passwords.
-


Why is Exclusive Or (XOR) Important in Cryptography?
Jan 18, 2020 by Lane WagnerIf you are getting into cryptography, or just trying to understand the fundamentals, you may have noticed that the exclusive or (XOR) operation is used quite often, especially in ciphers.
-


Cryptography Trends And News Going Into 2020
Jan 03, 2020 by Lane WagnerQuantum Computing 🔗 Quantum computing may not be coming quite as fast as some in the field had certainly feared (or perhaps hoped).
-
Intro to The AES-256 Cipher
Jan 02, 2020 by Lane WagnerAES, or “Advanced Encryption Standard”, is an encryption specification that uses the Rijndael cipher as its symmetric key ciphering algorithm.
-


(Very) Basic Intro to Hash Functions (SHA-256, MD5, etc)
Jan 01, 2020 by Lane WagnerHash functions are used to securely store passwords, find duplicate records, quickly store and retrieve data, among other useful computational tasks.
-


Basic Intro to Key Derivation Functions
Dec 30, 2019 by Lane WagnerA Key Derivation Function, or KDF, is a cryptographic algorithm that derives one or more secret keys from a secret value.
-


Cryptology vs Cryptography - Definitions and Differences
Dec 16, 2019 by Lane WagnerMany new developers are jumping right into writing code, usually for those fat paychecks, without learning much about the history of Computer Science.
-


Encoding vs Encryption - They Aren't the Same
Aug 14, 2019 by Lane WagnerWhile encryption does involve various methods of encoding data, the two are absolutely not interchangeable. In fact, if you get them mixed up it can result in serious data breaches and security vulnerabilities.